Expert penetration testing for AWS environments, from IAM to infrastructure
Our AWS penetration testing services identify real vulnerabilities across your Amazon Web Services environment. We go beyond automated scanning to manually test IAM policies, S3 bucket configurations, Lambda functions, EC2 instances, and cross-account trust relationships using the same techniques that real-world attackers employ.
Every engagement is led by AWS-certified security practitioners who map findings to the MITRE ATT&CK Cloud matrix and deliver actionable remediation guidance tailored to your architecture.
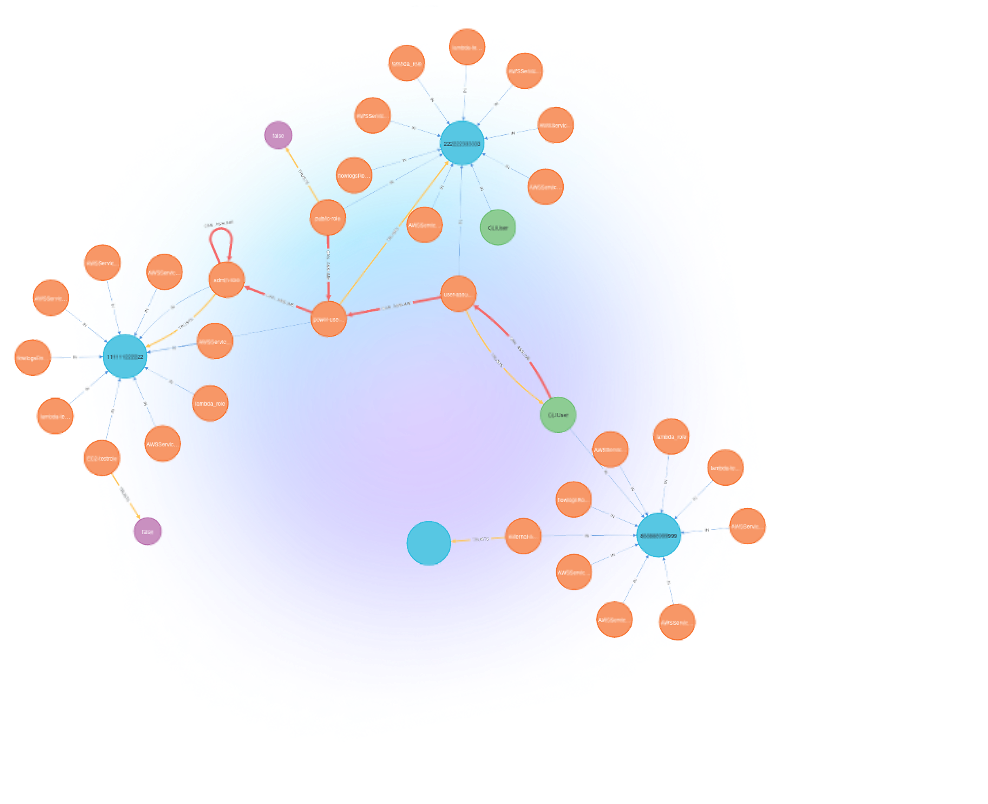
Expose privilege escalation paths and overly permissive IAM policies
We test your AWS IAM configuration for privilege escalation paths, overly permissive policies, cross-account trust abuse, role chaining vulnerabilities, and federation misconfigurations. Our testers evaluate IAM Access Analyzer findings, identify resource-based policy weaknesses across S3, SQS, SNS, and Lambda, and attempt lateral movement through AssumeRole chains and instance profile exploitation.
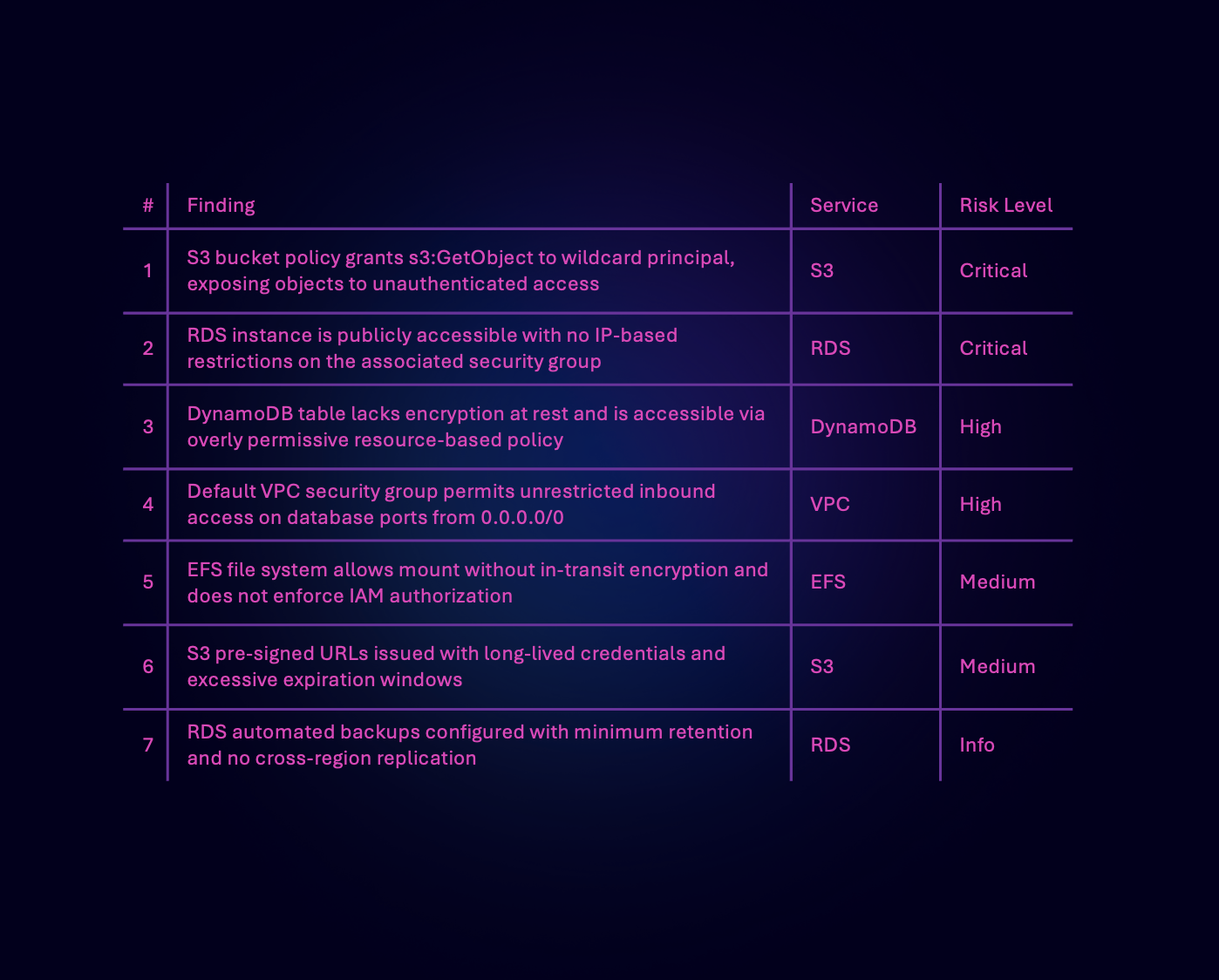
Find exposed buckets, misconfigured access controls, and data exfiltration paths
We assess your S3 buckets, DynamoDB tables, RDS instances, EFS shares, and other AWS data stores for access control weaknesses, encryption gaps, and data exposure risks. Our testing covers bucket policy misconfigurations, ACL bypass techniques, pre-signed URL abuse, cross-account access vulnerabilities, and data exfiltration paths through VPC endpoints, DNS tunnelling, and legitimate AWS services.

Test event-driven architectures, API Gateway, and serverless attack surfaces
Our testers evaluate Lambda functions, API Gateway configurations, Step Functions, and EventBridge rules for injection vulnerabilities, insecure environment variable handling, overly permissive execution roles, and event source manipulation. We assess serverless-specific risks including function chaining abuse, cold start exploitation, layer poisoning, and unauthorized invocation through misconfigured triggers and resource policies.

Structured, repeatable, and aligned with MITRE ATT&CK Cloud for AWS
Every AWS penetration test follows a structured methodology aligned with PTES, OWASP, and the MITRE ATT&CK Cloud matrix. We begin with threat modelling and scoping tailored to your AWS architecture, followed by reconnaissance, vulnerability identification, exploitation, and post-exploitation analysis that mirrors real adversary behaviour.
We go beyond automated scanning - our testers chain misconfigurations, abuse trust relationships, and exploit cloud-native features the way actual threat actors do. Deliverables include executive and technical reports with findings mapped to ATT&CK techniques and prioritised remediation guidance.
AWS security specialists who build, break, and defend cloud environments
Pwned Labs is not a traditional consultancy - we are practitioners who build, break, and defend AWS environments every day. Our penetration testers hold certifications including CREST CRT and AWS Security Specialty, and actively contribute to the offensive security community through research, tooling, and training content used by thousands of professionals worldwide.
Every engagement is led by operators with direct experience across Fortune 500 AWS environments, startups, and government agencies. We understand AWS-native threats because we research and simulate them daily on our own cloud security training platform.