Cloud penetration testing across AWS, Azure, GCP, and hybrid environments
Identify misconfigurations, privilege escalation paths, and attack vectors across your cloud infrastructure. Our cloud-specialized pentesters simulate real-world adversary techniques to expose risks before attackers do.
Identify risks across IAM, S3, Lambda, EC2, and more
Our AWS penetration testers evaluate your environment for misconfigurations, overly permissive IAM policies, exposed secrets, and privilege escalation paths that attackers exploit in the wild. We test across the full AWS attack surface including identity federation, cross-account trust relationships, serverless functions, container workloads, and data stores.
Every engagement maps findings to the MITRE ATT&CK Cloud matrix and AWS-specific threat models, giving your team actionable remediation guidance tied to real adversary techniques.
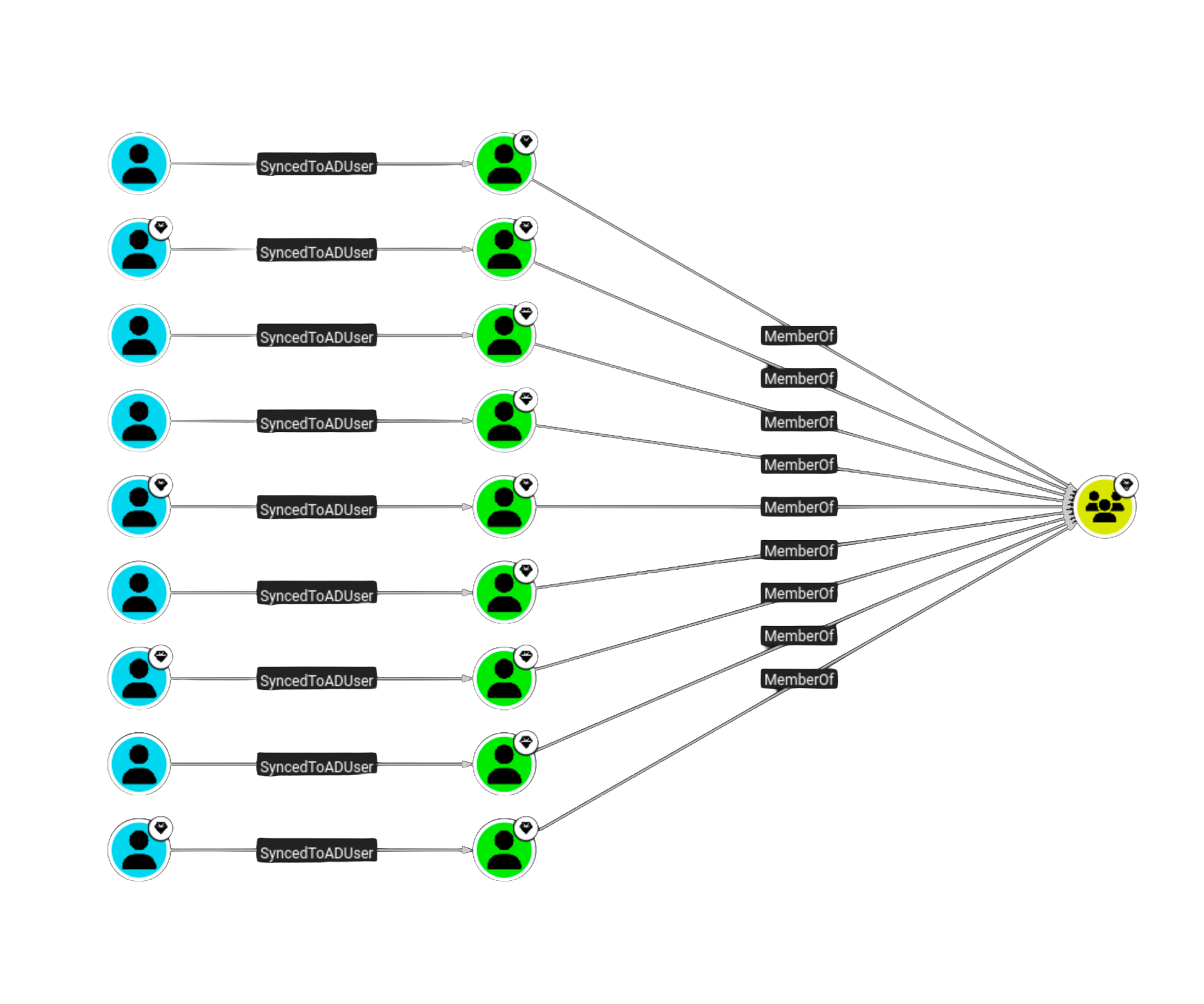
Entra ID, Azure AD, and hybrid environment testing
Azure environments introduce unique attack surfaces through Entra ID (formerly Azure AD), managed identities, role-based access control, and hybrid configurations that bridge on-premises Active Directory with cloud resources. Our testers specialize in Azure-specific attack chains including token theft, conditional access bypasses, and service principal abuse.
We assess Azure subscriptions, resource groups, storage accounts, Key Vault configurations, virtual networks, and App Service deployments to identify lateral movement paths and data exposure risks across your Azure footprint.

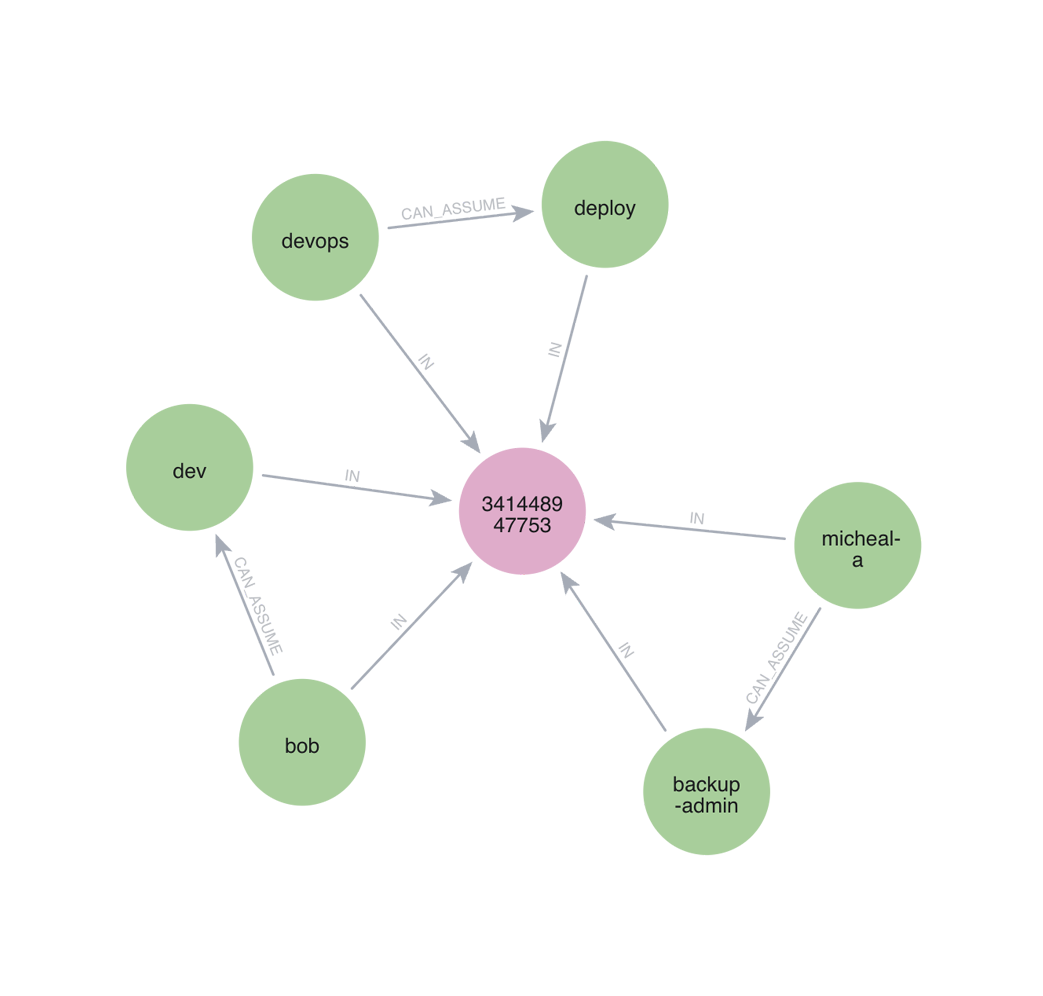
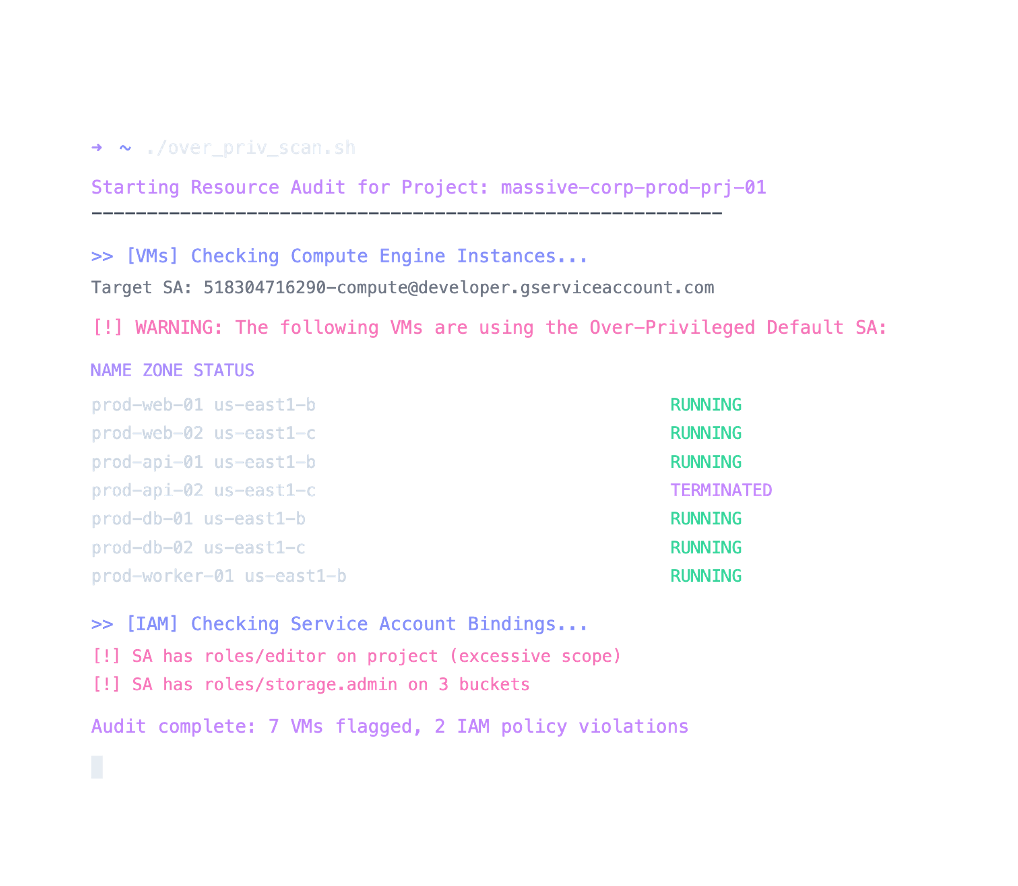
Google Cloud IAM, GKE, and service account exploitation
Google Cloud Platform presents distinct security challenges through its resource hierarchy, IAM bindings, service account key management, and Workload Identity Federation. Our GCP penetration testers assess your projects for overprivileged service accounts, misconfigured Cloud Storage buckets, exposed metadata endpoints, and GKE cluster weaknesses.
Engagements cover Compute Engine, Cloud Functions, Cloud Run, BigQuery, Pub/Sub, and VPC configurations. We map every finding to specific GCP security best practices and provide step-by-step remediation for your engineering teams.

Structured, repeatable, and aligned with real-world threats
Our cloud penetration testing methodology follows a structured approach aligned with PTES, OWASP, and MITRE ATT&CK Cloud. Each engagement begins with threat modeling and scoping tailored to your environment, followed by reconnaissance, vulnerability identification, exploitation, and post-exploitation analysis that mirrors real adversary behavior.
We go beyond automated scanning. Our testers chain misconfigurations, abuse trust relationships, and exploit cloud-native features the way actual attackers do. Every finding includes proof-of-concept evidence, risk context, and prioritized remediation guidance your teams can act on immediately.
Practitioner-led pentesting from real-world operators
Pwned Labs isn't a traditional consultancy - we're practitioners who build, break, and defend cloud environments every day. Our penetration testers hold certifications including CRT, AWS Security Specialty, and AZ-500, and actively contribute to the offensive security community through research, tooling, and training content used by thousands of professionals worldwide.
Every engagement is led by operators with direct experience across Fortune 500 environments, startups, and regulated industries. We deliver clear, actionable findings - not recycled scanner output - with risk-rated remediation guidance your engineering teams can implement immediately. Our clients return because we find what others miss and communicate it in a way that drives real security improvement.