Comprehensive cloud security assessments that find what scanners miss
Understand your true cloud security posture with an in-depth assessment covering IAM policies, network configurations, data protection, logging, and compliance alignment across AWS, Azure, and GCP. Our practitioner-led assessments go beyond automated checklists to evaluate how your cloud environment would withstand real-world attacks - delivering prioritized, actionable findings your team can implement immediately.
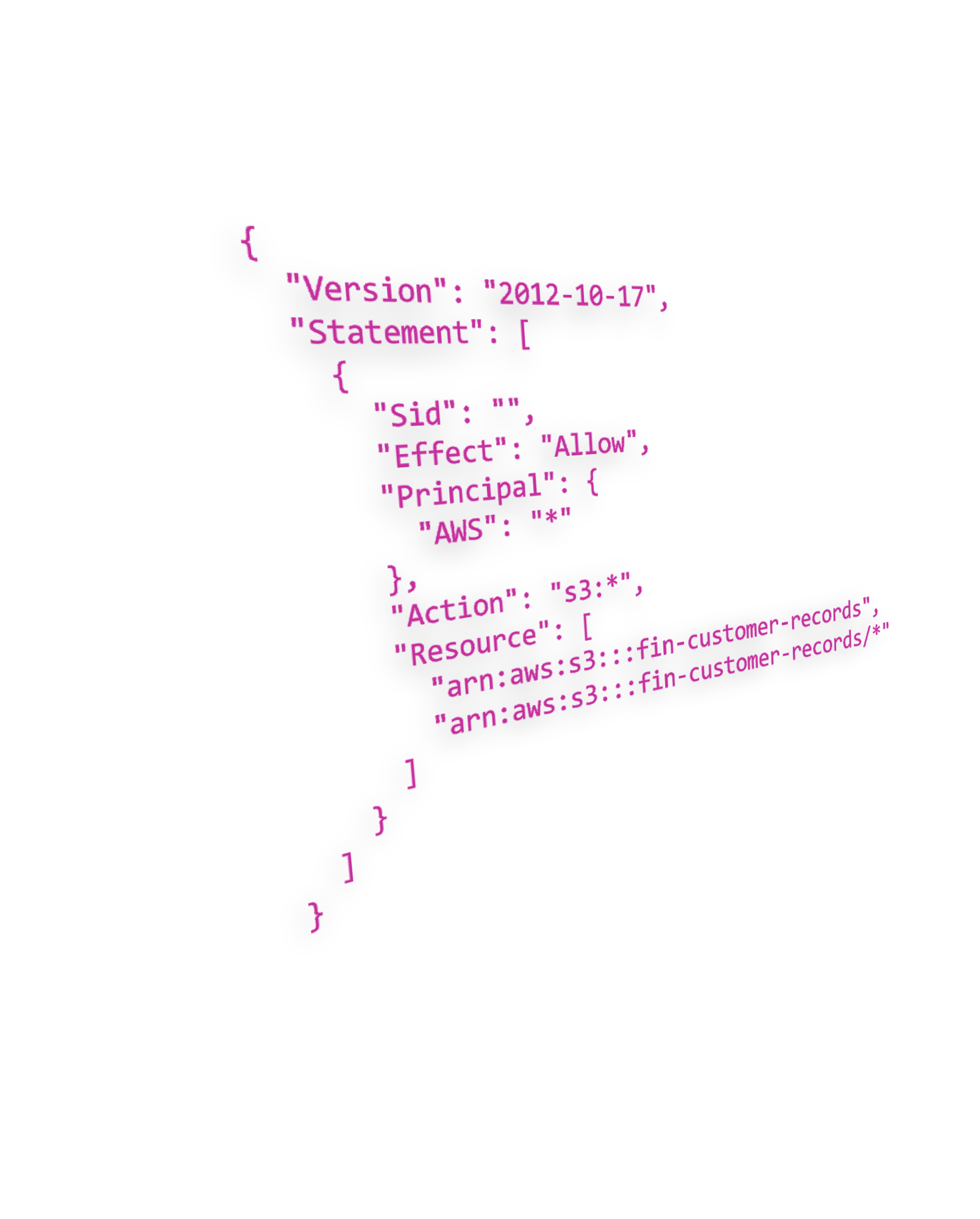
Audit IAM policies, roles, and permissions across your cloud estate
Our assessors systematically evaluate your IAM configurations to uncover overly permissive policies, unused credentials, excessive privilege assignments, and misconfigured trust relationships. We examine role chaining, cross-account access patterns, service control policies, and permission boundaries across AWS, Azure, and GCP to identify paths an attacker could exploit for lateral movement or privilege escalation.
You receive a prioritised findings report with clear remediation steps aligned to the principle of least privilege, helping your team lock down access before it becomes a breach vector.

Evaluate VPC design, network segmentation, and cloud architecture security
We review your cloud network architecture end to end - VPC and VNet configurations, subnet isolation, security group rules, network ACLs, peering connections, and transit gateway designs. Our assessors identify misconfigurations that could allow lateral movement between workloads, unintended internet exposure, or gaps in east-west traffic controls that automated scanners routinely miss.
The assessment covers hybrid connectivity, DNS security, load balancer configurations, and API gateway exposure across AWS, Azure, and GCP, delivering a detailed architecture risk map with actionable hardening recommendations.

Assess encryption standards, key management, and data classification controls
We evaluate how your organisation protects sensitive data at rest, in transit, and in use across cloud services. Our assessment examines encryption configurations for storage volumes, databases, object stores, and messaging queues, alongside key management practices in AWS KMS, Azure Key Vault, and GCP Cloud KMS to ensure keys are properly rotated, scoped, and access-controlled.
The review also covers data classification policies, DLP controls, backup encryption, and cross-region replication security - giving you confidence that your most critical assets are protected against both external threats and insider risk.

Practitioner-led assessments from real-world cloud security operators
Pwned Labs isn't a traditional consultancy - we're practitioners who build, break, and defend cloud environments every day. Our assessors hold certifications including CREST CRT, AWS Security Specialty, AZ-500, and CCSP, and bring direct experience from offensive security engagements across industries including finance, healthcare, SaaS, and government.
We also operate one of the world's leading cloud security training platforms, which means our assessment methodology is continuously refined against the latest attack techniques and misconfigurations we see in the wild.

Map your cloud security posture to industry standards and regulatory requirements
Our assessments map findings directly to the compliance frameworks that matter to your business - CIS Benchmarks, SOC 2, ISO 27001, NIST CSF, PCI DSS, and HIPAA. We identify control gaps across your cloud environment and provide evidence-ready documentation that supports audit preparation and regulatory reporting.
Whether you are preparing for your first SOC 2 audit or maintaining ongoing compliance across multiple frameworks, our assessment delivers a clear roadmap of what is in place, what is missing, and how to close the gaps efficiently.